Your cart is currently empty!
Author: Omar

Why Does IR Speed and Efficiency Fail Because of Compromised Identities?
Time is against incident response ( IR ). Because there is sufficient evidence that a negative event is occurring, you hire an internal or external team, but you are still unaware of its scope, effects, and underlying causes. Malicious files and outbound network connections can be found by IR teams thanks to a common set…

How to enable and disable private browsing in Safari
How to enable private browsing on an iPhone using Safari The steps listed below will help you enable private browsing on your iPhone: On your iPhone, open Safari. In the bottom-right corner of the screen, click the tabs button. Tap the” Private” tab group button by moving your finger there. The tab you want to…
Linux is introduced by Microsoft with the following commands: sudo ', Windows 11
12 February 2024 Newsroom Operating System/Technology To assist users in carrying out commands with administrator privileges, Microsoft announced the introduction of Sudo for Windows 11 in an early preview version. According to Microsoft Product Manager Jordi Adoumie,” Sudo for Windows is a new way for users to run elevated commands directly from an unelevated console…

Army Sergeant Monday’s Medal of Honor Long, Charles R.
Army Sergeant As his fellow soldiers fled a fierce enemy onslaught in Korea, Charles Richard Long offered to stay behind and protect their backs. He probably knew this was his last chance. He continued to serve honorably until he was no longer able to do so. He received the Medal of Honor for his bravery…

The United States offers a$ 10 million bounty in exchange for information that will result in the arrest of Hive ransomware leaders.
Up to$ 10 million in cash rewards have been announced by the U. S. Department of State for knowledge of people who hold important positions in the Hive ransomware scheme. Additionally, it is dispersing an additional$ 5 million in exchange for information that could result in the arrest and/or conviction of anyone” confederating with or…

Release notes for NordVPN for Linux
3. 17. 1 NordVPN With this update, NordVPN better aligns with your custom DNS preferences. If you’ve set your /etc/resolv.conf file to read-only, we will keep your DNS settings unchanged. We’ve been looking for bugs as usual to ensure that your NordVPN experience is as comfortable as possible. 3.17 NordVPN New: Custom nicknames can now…

Release notes for NordVPN for iOS
8. 22 NordVPN To make sure the statistics you see are always accurate, we’ve taken care of edge cases and minor bugs. More detailed information about your VPN usage is now available to you. 8.21 NordVPN By skipping the lengthy scroll, you can now quickly connect to the most well-liked locations by sorting the country…

How to check for and remove viruses on a Chromebook
Can Chromebooks get viruses? Yes, Chromebooks can get infected with viruses or malware if there is a breach of the system’s security when you fall for a phishing scam, install malicious apps and extensions, or practice unsafe online habits. Otherwise virus infections on Chromebooks are extremely rare because Chromebooks run the Google Chrome operating system,…
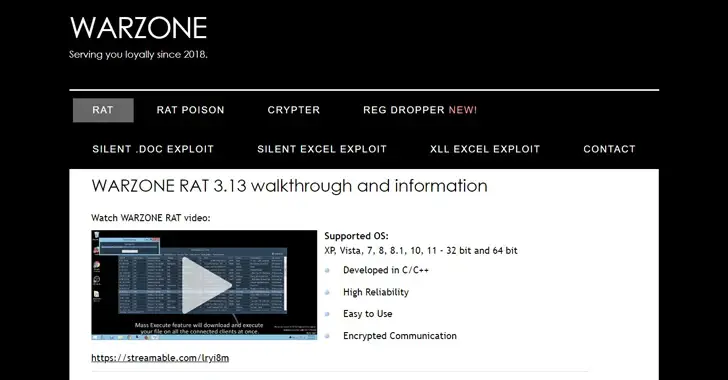
U. S. DoJ demolishes the Warzone RAT infrastructure and detains key operators.
11 February 2024 Newsroom Malware/Cybercrime The Warzone RAT remote access Trojan (RAT ) was being sold online, and the U.S. Justice Department ( DoJ) announced the seizure of that infrastructure on Friday. www. is one of the domains. [. ] warzone According to the DoJ, ws and three other individuals were “used to sell computer…

Online gambling in 2024: scopri the most widely dispersed and fair price for criminals
Truffe online: la situazione in Italia a inizio 2024 Nel report 2023 della Polizia Postale italiana si è registrato un significativo aumento dei casi di truffe ai danni di e-commerce e di falso trading online, con oltre 3.500 persone denunciate e un incremento del 20% delle somme sottratte rispetto al 2022, raggiungendo i 137 milioni…
