Your cart is currently empty!
Author: Omar
-

Advice for Customers on Emerging AnyDesk Cybersecurity Incident
A cyberattack in which hackers gained access to the company’s production environment has been confirmed by the remote desktop program AnyDesk. Since authentication tokens are only present on the end user’s device and are linked to the device by its fingerprint,  , Anydesk claimed that none were stolen during the attack. The company has, however,…
-

February 2, 2024, contracts
ARMY A$ 307, 200, 000 hybrid contract for software development, design, integration, testing, fielding, installation, management, and documentation was awarded to Shock Stream Phoenix Ventures LLC, * Oviedo, Florida. Six bids were received after being solicited online. Each order will have a specific work location and amount of funding, and it is anticipated to be…
-
Tucker Hamilton, an air force colonel, at altitude
Nine out of ten Americans are aware that artificial intelligence is used in their daily lives, according to a recent Pew Research study. 61 % of Americans 65 and older, as might be expected, are worried about AI’s expanding use.  , The fact that 42 % of Americans, aged 18 to 29, in the digital…
-

Week 5 of” The Good, the Bad, and the Ugly in Cybersecurity”
The Good: Modern Cyber Operations Disrupt Sophisticated Malware and Counter InsiderThreats This week, law enforcement organizations from all over the world took significant action to combat cyber threats in a number of cyber arrests and operations. Three former Homeland Security Department employees, including an Acting Inspector General, were sentenced in the United States for stealing…
-

Network Warfare and Swarm Geopolitics in the inaugural executive brief of PinnacleOne
The PinnacleOne Executive Brief has been re-launched. The P1 ExecBrief will offer useful insights on significant developments spanning geopolitics, cybersecurity, strategic technology, and related policy dynamics. It is designed for corporate executives and senior leadership in roles in risk, strategy, or security. We present our strategic analysis of the current geopolitical situation in our inaugural…
-

After a hacker stole data from millions of people and thousands of non-profits, the FTC slams Blackbaud for” shoddy security. “
In a damning post-mortem to the company’s data breach in February 2020, the United States Federal Trade Commission (FTC ) criticized the cybersecurity of data and software services provider Blackbaud as “lax” and” shoddy. “ The FTC claims that a hacker broke into Blackbaud’s customer databases in February 2020 and stole the personal information of…
-
According to the FBI, China is hacking Wi-Fi routers in order to attack the US water supply and electrical grid.
Have two and a half hours to spare? Perhaps you should watch this video from FBI director Christopher Wray warning the US Congress about the dangers posed by Chinese state-sponsored hackers rather than sitting down to watch” Mission: Impossible- Dead Reckoning Part One.” Law enforcement organizations have disrupted a botnet run by the Volt Typhoon…
-
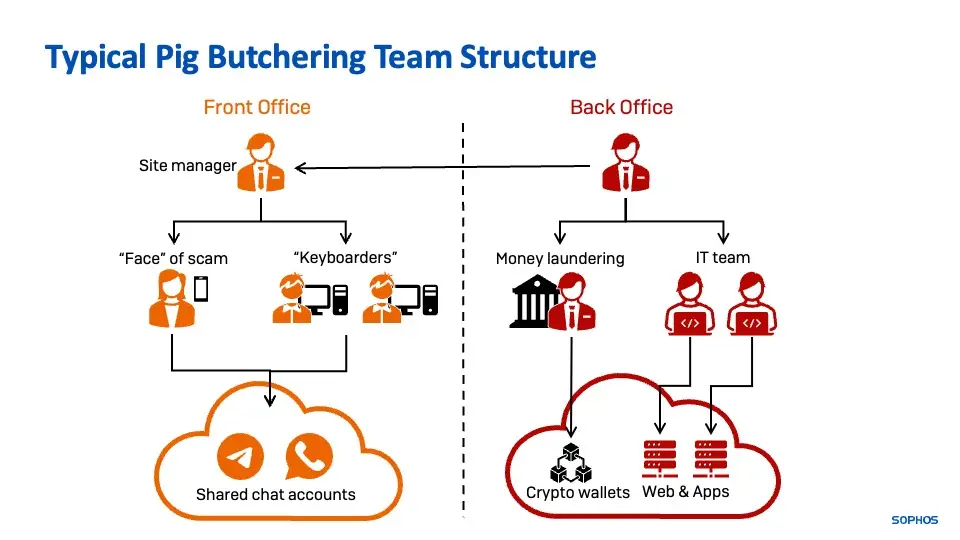
Scams involving cryptocurrencies proliferate in new ways.
Scams involving cryptocurrencies A recent retiree was sucked into what would turn out to be an exorbitantly expensive “relationship” in the spring of 2023. He was eventually persuaded to “invest” in what was described as “digital currency mining” after being lured by a dating application from someone who claimed to live in his area. In…
-

Installing a VPN on your router
What is a VPN router? A VPN router operates exactly as a regular VPN would. Your traffic is redirected to the servers of a VPN, which enables secure online browsing. All of your activities will be focused on the cualquiera that deals with espiarle, as well as large businesses that are devoted to facts. The…
-

Definition, erkennung, and protection of keyloggers
What exactly is a keylogger? A keylogger, also known as a tasten-rekorder, is software or hardware that is used for this purpose and that can be used to produce and protocollate tastes on demand, frequently without the user’s knowledge. While the technology is legal in and of itself, the majority of keyloggers are installed by…
