Your cart is currently empty!
Author: Omar
Microsoft mitigated exposure of internal information in a storage account due to overly-permissive SAS token
Summary Summary As part of a recent Coordinated Vulnerability Disclosure (CVD) report from Wiz.io, Microsoft investigated and remediated an incident involving a Microsoft employee who shared a URL for a blob store in a public GitHub repository while contributing to open-source AI learning models. This URL included an overly-permissive Shared Access Signature (SAS) token for…
Privacy Act; System of Records
Request Access Due to aggressive automated scraping of FederalRegister.gov and eCFR.gov, programmatic access to these sites is limited to access to our extensive developer APIs. If you are human user receiving this message, we can add your IP address to a set of IPs that can access FederalRegister.gov & eCFR.gov; complete the CAPTCHA (bot test)…

NIST Director Laurie E. Locascio to Lead Cybersecurity Business Development Mission to Taiwan
Between Sept. 18-20, Laurie E. Locascio, director of the Department of Commerce’s National Institute of Standards and Technology (NIST), will lead a cybersecurity business development mission to Taiwan. As the mission lead, Locascio will serve as the

Measuring the Accuracy of PCR Tests Can Improve Health Care Beyond COVID-19
Many of us have taken a COVID-19 test. But, have you ever wondered, after your sample goes off to a lab, exactly how they arrive at a positive or negative result?

Agents of Contrast, Software Runaway Hit, Our Early Universe: A Sample of Stories on NIST Social Media
Curious? It’s time to get you caught up on a few of the summer happenings at NIST.
NIST’s Planned Updates to Implementing the HIPAA Security Rule: A Cybersecurity Resource Guide
Background: NIST Special Publication (SP) 800-66 Healthcare organizations face many challenges from cybersecurity threats. This can have serious impacts on the security of patient data, the quality of patient care, and even the organization’s financial status. Healthcare organizations also must comply with regulatory requirements, such as the Health Insurance Portability and Accountability Act of 1996…

NIST to Standardize Encryption Algorithms That Can Resist Attack by Quantum Computers
Three new algorithms are expected to be ready for use in 2024. Others will follow.

FISSEA Summer Forum: August 23, 2023
The FISSEA Forums are quarterly meetings to provide opportunities for policy and programmatic updates, the exchange of best practices, and discussion and engagement among members of the Federal Information Security Educators (FISSEA) community. Agenda: 1:00pm-1:05pm FISSEA Welcoming Remarks Marian Merritt, NICE Deputy Director, National Institute of Standards and Technology 1:05pm-1:10pm Welcome and Event Logistics Kendra Henthorne,…
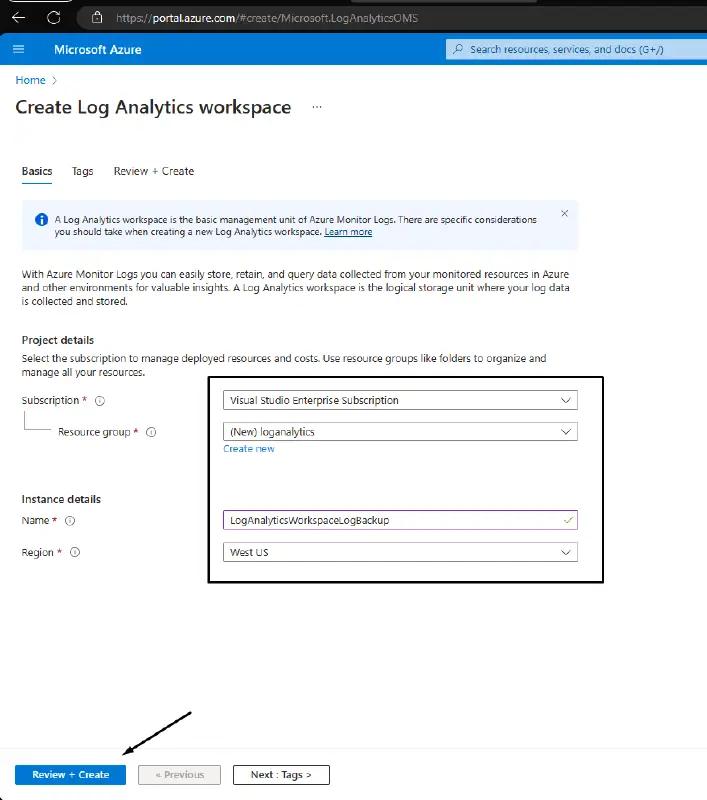
Part 1 of Azure’s Serial Console Attack and Defense
A virtual machine has ever crashed, right? A great way to connect to your virtual machine directly and troubleshoot is with Azure Serial Console. Everyone has access to the free Azure Serial Console feature. Although this feature’s main goal is to help users debug their computer, there are a number of intriguing ways to abuse…
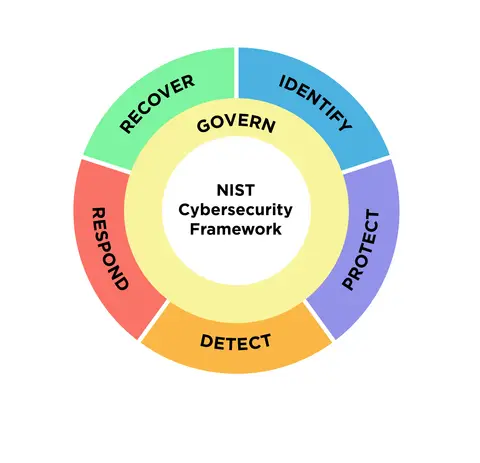
Major updates to NIST’s widely used cybersecurity framework are being developed.
The “govern” function, which emphasizes that cybersecurity is a significant source of enterprise risk and should be taken into account by senior leadership, has now been added to NIST’s list of the five essential components of an effective cybersecurity program. N. Hanacek/NIST for credit Since its debut almost ten years ago, the top cybersecurity advice…
