In the past 2 years, we have observed a significant surge in hacktivism activity due to ongoing wars and geopolitical conflicts in various regions. Since the war against Ukraine began, we have witnessed a notable mobilization of non-state and state-backed actors alike, forming new groups or joining existing hacker collectives.
We understand hacktivism as a form of computer hacking that is done to further the goals of political or social activism1. While activism describes a normal, non-disruptive use of the Internet in order to support a specific cause (online petitions, fundraising, coordinating activities), hacktivism includes operations that use hacking techniques with the intent to disrupt but not to cause serious harm (e.g., data theft, website defacements, redirects, Denial-of-Service attacks). Cyber operations that inherit a willingness or intent to cause harm to physical property, severe economic damage or loss of life would be referred to as cyberterrorism,2, 3 The lines between conducting cyber operations under the term of hacktivism and engaging in hostilities and causing severe damage and harm are becoming more and more blurry. With ongoing wars and conflicts, cyberspace has become messier than ever. We see a new leveling of the physical and cyber battlefields, resulting in a very thin line between physical (war) and cyber (hacktivism)4. As Dr Vasileios Karagiannopoulos and Professor Athina Karatzogianni put it:
“Contemporary events show us that hacktivism has become mainstream and is now an inevitable dimension of political conflicts, even those that end up in kinetic clashes between states, testing the virtual limits of symbolic, sensationalist hacks, vigilantism, cyber espionage, and even cyber warfare.5“
We began tracking some of the most active hacktivist groups in 2023. One factor that has increased transparency of ongoing hacktivism activity is visibility. We are now able to follow and subscribe to hacktivists’ communication channels.
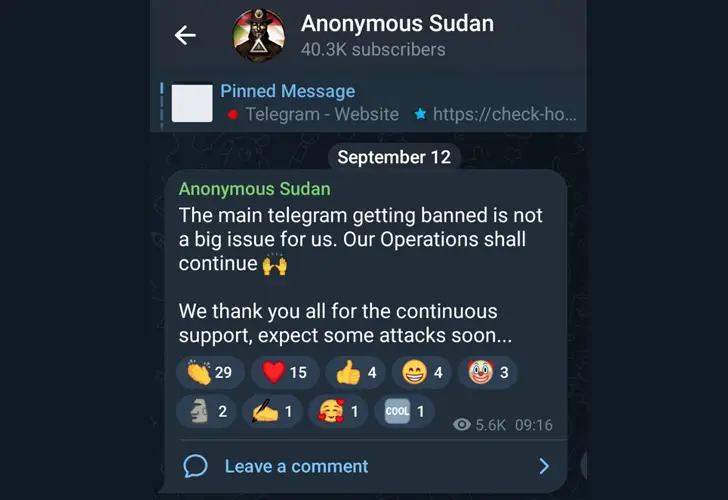
Telegram is a widely used messaging service misused by hacktivists6. While Telegram has attempted to counter malicious activities on its platform, they do face challenges many digital service providers face: the ability of abusers to return with a new user name, new channel name, or new account and continue as usual. Last September, Telegram banned the main channel of a hacktivist group called Anonymous Sudan, most likely based on their use of bots, not because of their engagement in various forms of cyber aggression. The group replied to this action with the following:
Another channel was created, and their activities continued. And so did many other operations under the disguise of hacktivism.
Hacktivists target private and Government organizations alike, and we have seen that hacktivist groups can take down even the biggest national or international websites. Some hacktivist groups have developed strong DDoS capabilities, while others are rather noisy about their capabilities and impact, applying a language and narrative that is disproportional to their actual action (and impact).
In both cases, the result is Fear, Uncertainty, and Doubt (FUD) – the escalation of anxiety, distrust, and disharmony – in an already tense and complex geopolitical context. Such FUD is emblematic of a continuous evolution towards ‘cognitive’ attacks, which seek to shape perception through technical activity. The impact has less to do with the disruptive effect of the attack or the value of the data or systems that may be affected (e.g., stolen, leaked, or destroyed) but with the impact that the attacks have on societal perception, discourse, and policy.
Hacktivist activity in 2023
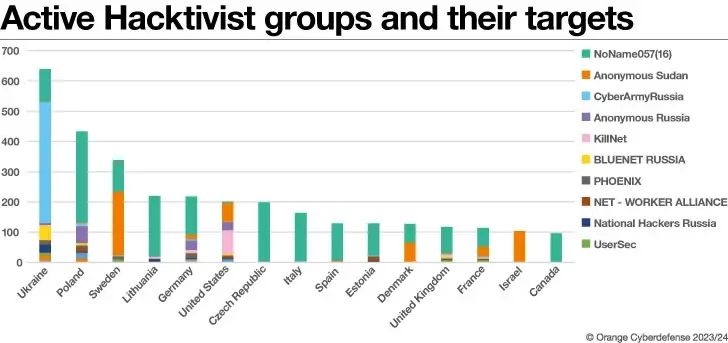
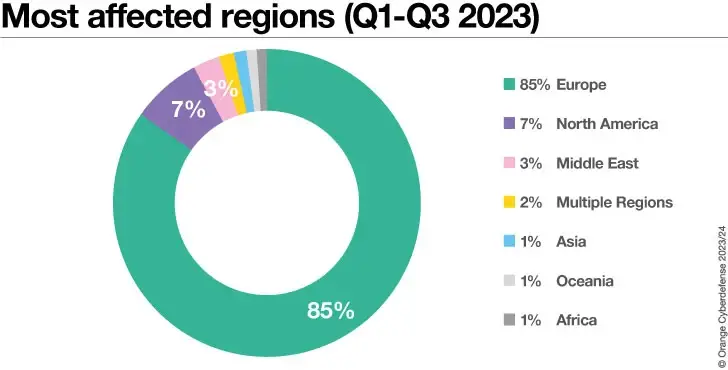
During the first three quarters of 2023, most of the hacktivism activity observed in 2023 (n=4016) originated from the war against Ukraine, and we saw Europe as a geographical region mostly impacted. We witnessed how proclaimed attacks against “the West” were a common narrative that we observed by pro-Russian hacktivist groups. Therefore, our focus became to monitor some of the very active, pro-Russian hacktivist groups.
Countries that were impacted the most by pro-Russian hacktivist attacks were Ukraine, Poland and Sweden. The highest level of hacktivism activity we have seen was in February 2023. This corresponds with the emergence of the hacktivist group Anonymous Sudan at the end of January 2023, which heavily targeted countries in the Nordics but later moved on to other regions in the world.
The focus on Ukraine is simply understood as the use of hacktivism as a tool in the war with Russia. The second most impacted country was Poland, which could be explained by Poland’s geographical closeness to the war. Sweden has been the third most impacted country since the beginning of 2022. However, Sweden only emerged in our data between January and March 2023, when the hacktivist group Anonymous Sudan heavily attacked Sweden and Denmark.
How politically consistent are these groups?
Two pro-Russian hacktivist groups that impacted the private and public sectors alike in 2023 were NoName057(16) and Anonymous Sudan. Anonymous Sudan is a very inconsistent threat actor. Our observations show that they have attacked victims all around the world, shifting their purported motivations and reasonings frequently. Despite the apparent identity crisis, the group has proven to be capable, not only technically, but also at making noise and seeking attention. But while they have made a name for themselves with their volume of activity in 2023, their claims often exceed the real impact of their attacks7. In the end, they are dependent on media attention and thrive on the attention of the wider public. The other hacktivist group we have been observing during 2023 is NoName057(16). NoName057(16) might be more politically consistent than Anonymous Sudan has proven to be.
Security Navigator 2024 is Here – Download Now#
The newly released Security Navigator 2024 offers critical insights into current digital threats, documenting 129,395 incidents and 25,076 confirmed breaches. More than just a report, it serves as a guide to navigating a safer digital landscape.
What’s Inside?#
- 📈 In-Depth Analysis: Explore trends, attack patterns, and predictions. Learn from case studies in CyberSOC and Pentesting.
- 🔮 Future-Ready: Equip yourself with our security predictions and research summary.
- 👁️ Real-Time Data: From Dark Net surveillance to industry-specific statistics.
Stay one step ahead in cybersecurity. Your essential guide awaits!
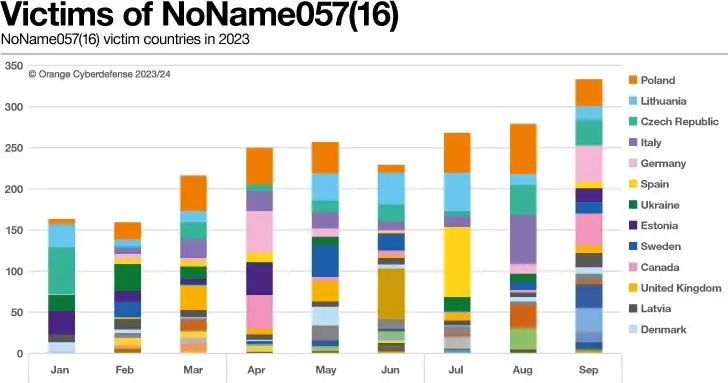
NoName057(16) has been active since the war against Ukraine began and has been targeting countries that are members of the the North Atlantic Treaty Organization (NATO) and countries that are considered to oppose Russian interests. By monitoring the publicly available Telegram messages on the English-speaking channel of NoName057(16) Eng, we deduce that the group specifically and directly impacts countries that are providing aid to Ukraine in the ongoing war.
Political hacktivism as a ‘proportionate’ response
Using an external dataset that has collected official announcements of countries committing to support Ukraine, we can correlate NoName057(16)’s attacks against the specific countries providing the promised support.
For this purpose, we use the Ukraine support tracker database that has been created and is regularly updated by the Kiel Institute for the World Economy8. The institute began tracking government-to-government (bilateral) commitments to Ukraine on January 24, 2022, by at least 40 different governments and continuously doing so at the time of writing.
The Ukraine support tracker shows that the United States has provided the most aid to Ukraine. In fact, they have committed (though not yet completely delivered) more support to Ukraine than all EU countries combined.
Noteworthy, besides the documented aid provided by the respective countries listed, a paper published9 alongside the Ukraine aid tracker database points out that the overall support given to Ukraine could be bigger when compared to support given in other wars in history.
As the paper states:
“The results show that governments in Europe did announce very large emergency funds in response to the war and energy price spike, but the bulk of the announced support was pledged to support their own households and firms rather than to support Ukraine. In total, the domestic energy support package commitments announced by EU countries amount to €570 billion, compared to €55 billion in total EU commitments to Ukraine.”
This is particularly interesting considering the perceived high level of aid provided that is created by news outlets. The activities of NoName057(16) appear to track media trends and can seem disproportionate when this aid is put into a historical context.
So how does NoName057(16)’s victimology look in comparison to the level of support provided by governments as tracked by the Ukraine aid tracker project?
As can be seen above, victimology is very diverse in terms of which country is impacted. In total, since they became active, NoName057(16) has impacted 38 different countries. The top 5 countries impacted in 2023 (Q1 – Q3) were Poland, Lithuania, Czech Republic, Italy and Spain. Ukraine is only at position #6 in NoName057(16)’s list of victims, which is interesting given the fact that Ukraine is the target country in the physical war.
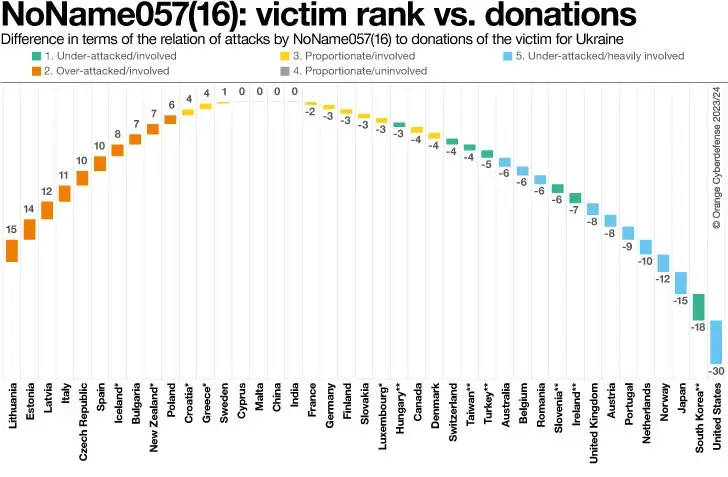
Let’s explore whether we can find a reasonable explanation for NoName057(16)’s choice of victim countries in the Ukraine support tracker database. For this, we conducted an experiment that looks at the countries that are noted by the Ukraine support tracker. We rank those countries by how much support (in terms of billions of USD) countries have promised to aid Ukraine (as visualized earlier). We then overlay this with the NoName057(16) country victim list, adding a ranking to reflect who has been attacked the most. Using the ranking of countries in each list, we calculate the distance between the two rankings.
In our experiment, a distance of “0” could be considered to signal a politically “proportionate” response by NoName057(16), indicating that the country’s ranking as a victim corresponds with its ranking in terms of the level of support offered. We increase the radius to consider countries with distances between -4 and 4 as the “proportionate” victims.
A negative distance tells us that those countries have made promises to support Ukraine but have not experienced correspondingly high numbers of attacks by NoName057(16). These countries are thus underrepresented in the NoName057(16) victim data. A positive distance suggests the opposite: These countries have been attacked many times by NoName057(16), but have not committed equivalently significant support to Ukraine. These countries are thus overrepresented in the NoName057(16) victim data.
If we look at examples of this logic at both extremes, we can identify the countries that appear “under-attacked”, those that appear “over-attacked“with respect to the level of support they have promised Ukraine, and those where the level of attack could be viewed as political “proportionate” from the hacktivist perspective.
But there are other groups of countries that emerge from this insight:
- Under-attacked and involved: Some countries have indeed committed to supporting Ukraine but were never impacted by attacks from NoName057(16).
- **Those countries include South Korea, Ireland, Slovenia, Turkey, Taiwan, and Hungary.
- Over-attacked: Some countries appear to have suffered a disproportionate level of attack relative to the amount of support they have offered. The countries include Lithuania, Estonia, Latvia, Italy and Czech Republic, Spain, and Bulgaria.
- *Iceland and New Zealand also technically fall into this group, but their victim counts and promised support levels are so low that their position in our analysis is exaggerated.
- Proportionate and involved: Sweden, France, Germany, Finland, Slovakia, Canada, Denmark and Switzerland have all been heavily impacted by attacks, but the relative volume of attacks correlates logically with the relatively high level of aid provided to Ukraine. These countries could be thought of as the major ‘front’ in NoName’s hacktivist war.
- *The impact on Greece, Croatia and Luxembourg is also technically ‘logical’ in that it corresponds with the level of aid provided, but it should be noted that the levels of impact and the levels of aid are both substantially lower than the other countries in this group.
- Proportionate but uninvolved: Some countries have not been impacted by attacks at all, and have not pledged to support Ukraine. These include Cyprus, Malta, China, and India. The impact on this group is politically “logical”, but essentially irrelevant.
- Under-attacked but heavily involved: The countries in this group include the United States, Japan, Norway, Netherlands, Portugal, Austria, the United Kingdom, Romania, Belgium and Australia. These countries have indeed been impacted by attacks, but the relative level of attacks they experience is low relative to the level of aid they have offered. The level of focus by NoName on this group is therefore also politically “disproportionate”, with the United States standing far beyond others in this group from this perspective. The same analysis, but using a percentage of GDP as the measure of aid given (rather than pure USD), would place Norway as the stand-out in this group.
We observe that most of the over-attacked countries are geographically relatively close to the war, which could be the main reason for their apparent “unfair treatment.” This aligns with the findings of the paper published with the Ukraine support tracker, in which the authors highlight that Eastern European countries stand out in terms of the help provided as a percentage of their GDP, especially when factoring in the costs of hosting war refugees10. Thus, geographical proximity and the appearance of “hands-on” support could explain why some countries are impacted more than seems “proportionate.” The exceptions here appear to be Spain and Italy, both of which suffer relatively high levels of attack despite relatively low levels of promised support but are not in close geographical proximity to the conflict.
Our qualitative observation of respective Telegram channels suggests that NoName057(16) has mostly been attacking Spain due to the military support and military training offered, along with the sanctions they’ve imposed.
Italy seems to be the victim of similar reasoning to Spain, in which they are apparently attacked due to military aid provided. There seems to be a misconception by NoName057(16) that Italy and Spain are large donors to Ukraine. As the Ukraine Support Tracker authors state: “In international comparison, it is puzzling why some rich Western European countries, like France, Italy, or Spain, provide so little bilateral support11.”
This is another excerpt of our analysis. An analysis of the threat potential of Cyber Warfare and its main actors (as well as a ton of other interesting research topics like an analysis of the data obtained from our extensive vulnerability management operations and Cyber Extortion statistics) can be found in the Security Navigator. Just fill in the form and get your download. It’s worth it!
Researcher notes – Data Source
Intel471: We thank Intel471 for their specialist contribution of data on overall activity & country distribution of pro-Russian hacktivist groups.
Telegram scraper: OCD capabilities
According to the Ukraine Support Tracker:
- “We considered 2242 formal announcements of support between Dec 2021 and July 2023.
- Data included commitments from 41 donors, including G7 and EU member countries, plus Australia, New Zealand, Norway, South Korea, Switzerland, Turkey, India, China and Taiwan. Additionally, aid from EU institutions is traced, such as European Union institutions, meaning the EU Commission and EU Council, but also via the European Peace Facility (EPF) and the European Investment Bank (EIB).
- The type of aid is classified into three types: military, humanitarian, and financial.
- We removed entries that were not an official announcement but where support was mentioned by government officials (e.g., Minister of Foreign and European Affairs) during conferences, summits, etc. We limited our analysis to official announcements that then caused a direct response by specific hacktivist groups. The official website of the Ukrainian Government describes additional financial aid, so that data was also considered but with a later time stamp. Support for NATO is not included in this dataset, which hacktivists also reacted on“.
References:
- https://www.techtarget.com/searchsecurity/definition/hacktivism
- Denning, Dorothy. (2000). Activism, Hacktivism, and Cyberterrorism: The Internet as a Tool for Influencing Foreign Policy. Networks and Netwars: The Future of Terror, Crime, and Militancy. 248.
- Samuel, Alexandra Whitney (2004), Hacktivism and the Future of Political Participation, Harvard University.
- https://www.securityinfowatch.com/cybersecurity/article/53056804/did-the-russiaukraine-war-start-a-hacktivist-revolution
- https://engelsbergideas.com/essays/hacktivisms-cold-war-turns-hot/
- https://www.bleepingcomputer.com/news/security/hacktivists-cybercriminals-switch-to-telegram-after-russian-invasion/
- https://cip.gov.ua/services/cm/api/attachment/download?id=60068
- https://www.ifw-kiel.de/topics/war-against-ukraine/ukraine-support-tracker/
- https://www.ifw-kiel.de/topics/war-against-ukraine/ukraine-support-tracker/
- https://www.ifw-kiel.de/publications/the-ukraine-support-tracker-which-countries-help-ukraine-and-how-20852/
- https://www.ifw-kiel.de/publications/the-ukraine-support-tracker-which-countries-help-ukraine-and-how-20852/
Note: This informative piece has been expertly crafted and contributed by Diana Selck-Paulsson, Lead Security Researcher at Orange Cyberdefense.