Security researcher HaxRob discovered a previously unknown Linux backdoor named GTPDOOR, designed for covert operations within mobile carrier networks.
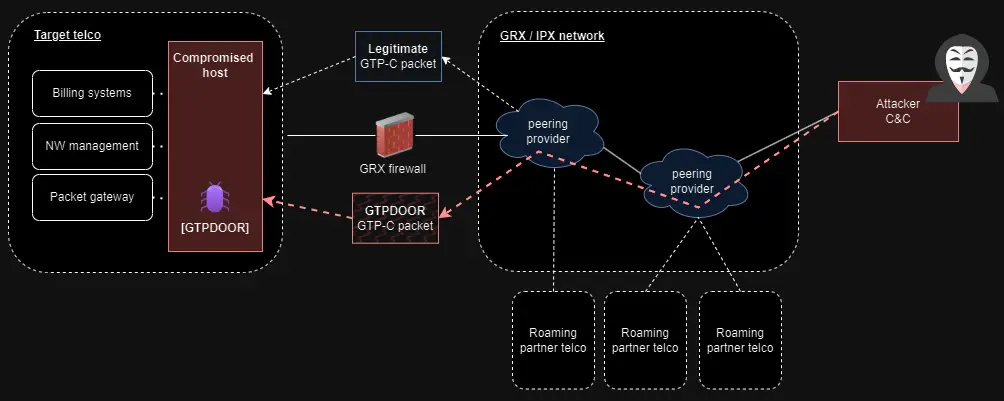
The threat actors behind GTPDOOR are believed to target systems adjacent to the GPRS roaming eXchange (GRX), such as SGSN, GGSN, and P-GW, which can provide the attackers direct access to a telecom’s core network.
The GRX is a component of mobile telecommunications that facilitates data roaming services across different geographical areas and networks. While the Serving GPRS Support Node (SGSN), Gateway GPRS Support Node (GGSN), and P-GW (Packet Data Network Gateway (for 4G LTE) are components within a mobile operator’s network infrastructure, each serving different roles in mobile communications.
As the SGSN, GGSN, and P-GW networks are more exposed to the public, with IP address ranges listed in public documents, the researcher believes they are the likely target for gaining initial access to the mobile operator’s network.
In his write-up, HaxRob explained that GTPDOOR is likely a tool belonging to the ‘LightBasin’ threat group (UNC1945), notorious for intelligence-collection operations targeting multiple telcos worldwide.
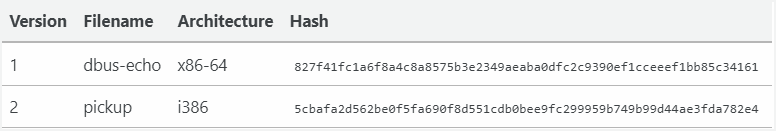
The researcher discovered two versions of the backdoor uploaded to VirusTotal in late 2023, both passing largely undetected by antivirus engines. The binaries targeted a very old Red Hat Linux version, indicating an outdated target.
The stealthy GTPDOOR operation
GTPDOOR is a sophisticated backdoor malware tailored for telecommunications networks, leveraging the GPRS Tunnelling Protocol Control Plane (GTP-C) for covert command and control (C2) communications.
It is designed for deployment in Linux-based systems adjacent to the GRX, responsible for routing and forwarding roaming-related signaling and user plane traffic.
Using GTP-C for communication allows GTPDOOR to blend with legitimate network traffic and utilize already permitted ports that aren’t monitored by standard security solutions. For additional stealth, GTPDOOR can change its process name to mimic legitimate system processes.
The malware listens for specific GTP-C echo request messages (“magic packets”) to wake up and execute the given command on the host, sending the output back to its operators.
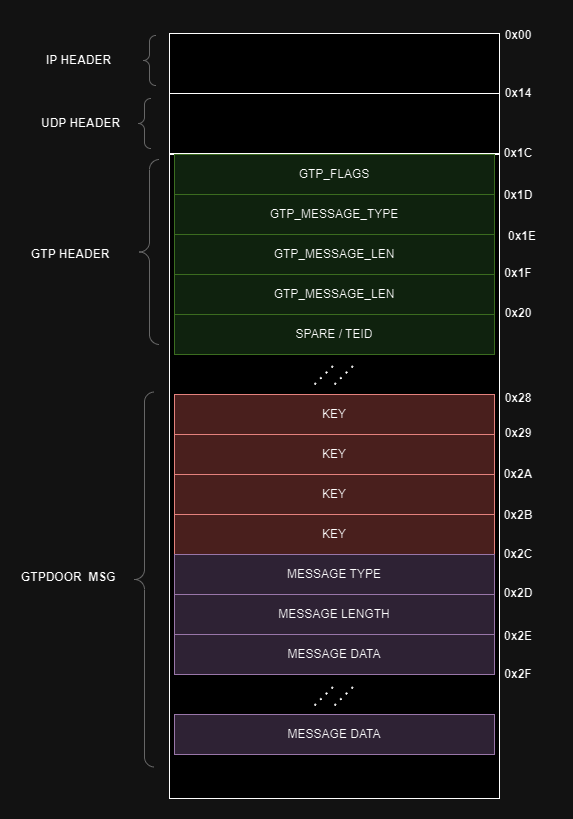
The contents of the magic GTP packets are authenticated and encrypted using a simple XOR cipher, ensuring that only authorized operators can control the malware.
GTPDOOR v1 supports the following operations on breached hosts:
- Set a new encryption key used for C2 communications
- Write arbitrary data to a local file named ‘system.conf’
- Execute arbitrary shell commands and send back the output
GTPDOOR v2 supports the above operations plus the following:
- Specify IP addresses or subnets allowed to communicate with the compromised host through an Access Control List (ACL) mechanism.
- Retrieve the ACL list to make dynamic adjustments to the backdoor’s network permissions.
- Clear ACL to reset the malware
HaxRob also highlights the malware’s ability to be covertly probed from an external network, eliciting a response via a TCP packet passed through any port.
Detection and defense
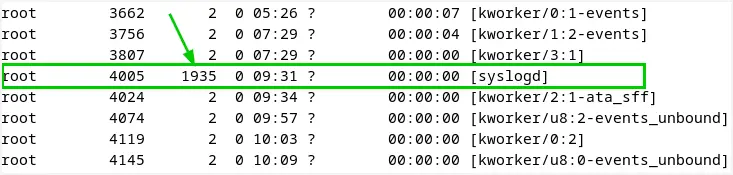
Detection strategies involve monitoring for unusual raw socket activities, unexpected process names, and specific malware indicators such as duplicate syslog processes.
The recommended detection steps are the following:
- Check for open raw sockets with lsof, indicating a potential breach.
- Use netstat -lp –raw to find unusual listening sockets.
- Identify processes mimicking kernel threads with abnormal PPIDs.
- Search for /var/run/daemon.pid, a mutex file used by GTPDOOR.
- Look for an unexpected system.conf file, possibly created by the malware.
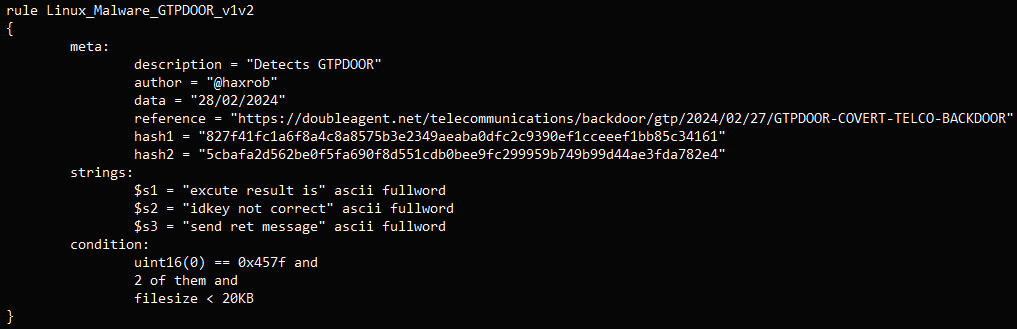
The following YARA rule for defenders to detect the GTPDOOR malware has also been provided.
Finally, the researcher proposes defense measures such as GTP firewalls with strict rules and adherence to GSMA security guidelines (1, 2) to block or filter out malicious packets and connections.