Mar 01, 2024NewsroomPhishing Kit / Cryptocurrency
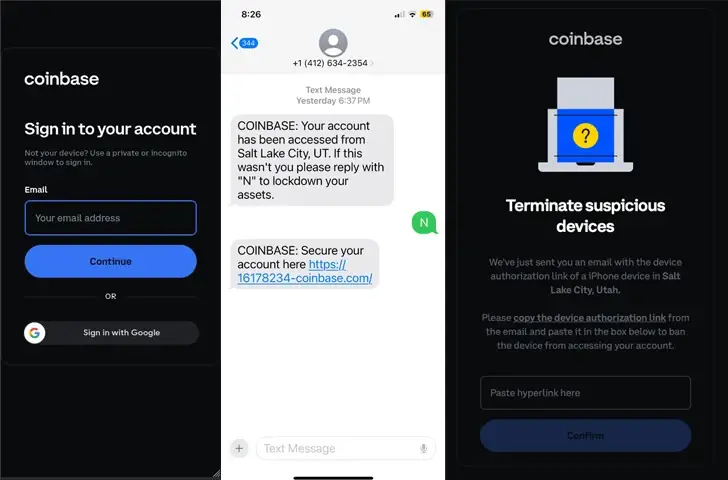
A novel phishing kit has been observed impersonating the login pages of well- known cryptocurrency services as part of an attack cluster designed to primarily target mobile devices.
” This kit enables attackers to build carbon copies of single sign- on ( SSO ) pages, then use a combination of email, SMS, and voice phishing to trick the target into sharing usernames, passwords, password reset URLs, and even photo IDs from hundreds of victims, mostly in the United States”, Lookout said in a report.
Targets of the phishing kit include employees of the Federal Communications Commission (FCC), Binance, Coinbase, and cryptocurrency users of various platforms like Binance, Coinbase, Gemini, Kraken, ShakePay, Caleb &, Brown, and Trezor. More than 100 victims have been successfully phished to date.
The phishing pages are designed such that the fake login screen is displayed only after the victim completes a CAPTCHA test using hCaptcha, thus preventing automated analysis tools from flagging the sites.
In some cases, these pages are distributed via unsolicited phone calls and text messages by spoofing a company’s customer support team under the pretext of securing their account after a purported hack.
Once the user enters their credentials, they are either asked to provide a two- factor authentication ( 2FA ) code or asked to “wait” while it claims to verify the provided information.
” The attacker likely attempts to log in using these credentials in real time, then redirects the victim to the appropriate page depending on what additional information is requested by the MFA service the attacker is trying to access”, Lookout said.
The phishing kit also attempts to give an illusion of credibility by allowing the operator to customize the phishing page in real- time by providing the last two digits of the victim’s actual phone number and selecting whether the victim should be asked for a six or seven digit token.
The one- time password ( OTP ) entered by the user is then captured by the threat actor, who uses it to sign in to the desired online service using the provided token. In the next step, the victim can be directed to any page of the attacker’s choosing, including the legitimate Okta login page or a page that displays customized messages.
Lookout said the campaign shares similarities with that of Scattered Spider, specifically in its impersonation of Okta and the use of domains that have been previously identified as affiliated with the group.
” Despite the URLs and spoofed pages looking similar to what Scattered Spider might create, there are significantly different capabilities and C2 infrastructure within the phishing kit”, the company said. ” This type of copycatting is common amongst threat actor groups, especially when a series of tactics and procedures have had so much public success”.
It’s currently also not clear if this is the work of a single threat actor or a common tool being used by different groups.
” The combination of high quality phishing URLs, login pages that perfectly match the look and feel of the legitimate sites, a sense of urgency, and consistent connection through SMS and voice calls is what has given the threat actors so much success stealing high quality data”, Lookout noted.
The development comes as Fortra revealed that financial institutions in Canada have come under the target of a new phishing- as- service ( PhaaS ) group called LabHost, overtaking its rival Frappo in popularity in 2023.
LabHost’s phishing attacks are pulled off by means of a real- time campaign management tool named LabRat that makes it possible to stage an adversary- in- the- middle ( AiTM) attack and capture credentials and 2FA codes.
Also developed by the threat actor is an SMS spamming tool dubbed LabSend that provides an automated method for sending links to LabHost phishing pages, thereby allowing its customers to mount smishing campaigns at scale.
With features ranging from ready-to-use templates to real-time campaign management tools and SMS lures,” LabHost services allow threat actors to target a variety of financial institutions,” according to the company.