Malicious JavaScript code hidden in a Tornado Cash governance proposal has been leaking deposit notes and data to a private server for almost two months.
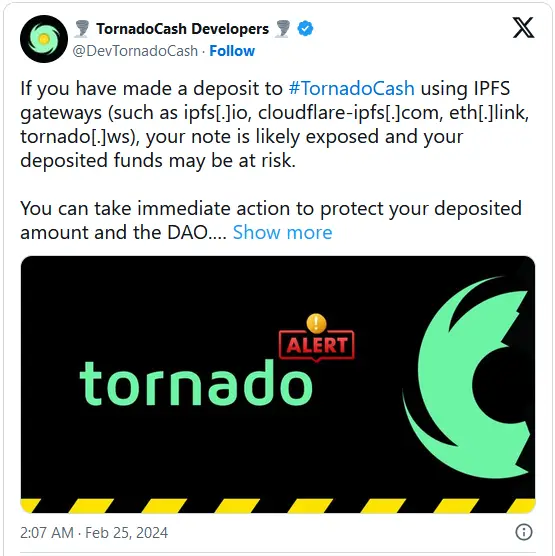
This leak compromises the privacy and security of all fund transactions made through IPFS deployments, such as ipfs. io, cf- ipfs.com, and eth. link gateways , since January 1.
A security researcher using the nickname Gas404 , discovered and reported the malicious code, urging , stakeholders to veto the malicious governance proposals.
Tornado Cash is a decentralized, open- source mixer , on the Ethereum blockchain that provides privacy for transactions through non- custodial, trustless, and serverless anonymization.
It uses a cryptographic zero- knowledge system named SNARKs ( Zero- Knowledge Succinct Non- Interactive Argument of Knowledge ) to allow users to deposit and withdraw funds anonymously.
Apart from users with legitimate reasons to protect their transactions from outside observers, Tornado Cash has also been used for money laundering.
The use of the mixer for illegal purposes led to , sanctions , in the United States in 2022 and the project’s founders were charged , in 2023 for helping criminals launder over$ 1 billion worth of stolen cryptocurrency.
Planting malicious code
Governance proposals in decentralized autonomous organizations ( DAOs ) like Tornado Cash are fundamental mechanisms for setting strategic directions, introducing updates, and modifying the core of the technical protocols.
They are submitted by token holders on the chain and are subsequently discussed and voted on by the project’s community. If accepted, the proposals are implemented into the protocol.
In the case of the Tornado Cash compromise, malicious JS code was introduced two months ago via a governance proposal ( number 47 ) from’ Butterfly Effects ‘- allegedly a community developer, and modified the protocol to leak deposit notes to the attacker’s server.
Gas404 says , that the malicious function encodes the private deposit notes to make them appear like regular blockchain transaction call data and hides the use of the ‘ window. fetch’ function to further obfuscate the exploitation mechanism.
The Tornado Cash Developers confirmed the compromise and warned about the risks, advising users to withdraw their old and possibly exposed notes and replace them with newly generated ones.
Also, token holders with voting rights were advised to cancel their votes for proposal 47 to revert the protocol changes and remove the malicious code.
This will not eliminate , the leak of the sensitive data, though. To mitigate the risk, Gas404 advises potentially exposed users to switch to a specific IPFS ContextHash deployment previously recommended and verified through Tornado Cash governance.